Continuously monitor your attack surface for risks with automated and manual penetration testing from Halo Security.
Get Started Free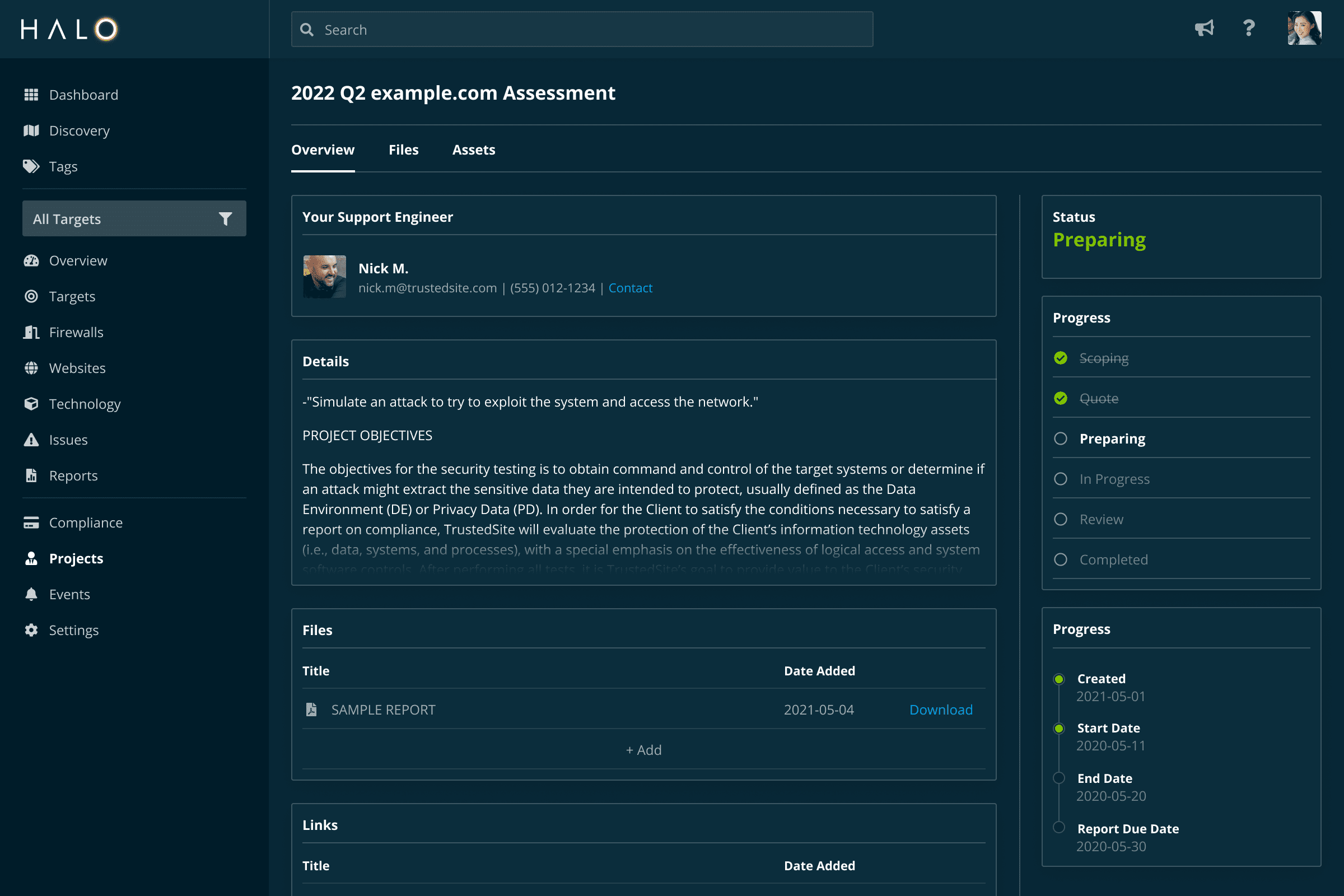
In today’s world, businesses face a growing risk of data exposure. Between a staggering number of security vulnerabilities, and an increasing dependence on externally managed assets, attackers have more pathways to reach sensitive data than ever before, and they’re constantly on the lookout for them.
Unfortunately, many organizations aren’t keeping as watchful of an eye for risk on their perimeter as the attackers. Manual penetration tests are often only performed once per year, but when new risks arise in the interim, it’s likely that no one will know until months, or even years, down the line, long after an attacker could have done their damage.
Here’s the thing about manual penetration testing. We believe it has an important role to play in every organization’s security program. In fact, it’s a service we ourselves offer at Halo Security, because some security issues can only be recognized by human intelligence.
But, it’s not a catch-all solution. Manual penetration tests tend to be too expensive to run every time the attack surface changes. That means some assets may not get tested at all, and others aren’t tested frequently enough, which leaves ample opportunity for attacks and highly exploitable vulnerabilities to go undetected.
Manual penetration testing is also time consuming. Testers are often forced to spend valuable time looking for common vulnerabilities that could have been detected far more efficiently with automated tools, which means they have less time to spend looking for the more complex vulnerabilities that require human expertise and experience.
By implementing automated penetration testing and vulnerability scanning tools, you can make manual penetration testing efforts more efficient and fill in any gaps they may leave behind. Automated penetration testing is designed to run on a continuous basis, so you can get instantly alerted whenever an issue is detected. And since automated tools are always monitoring for the easy-to-find issues, when you do hire manual penetration testers, they can focus more of their time looking for the issues that only an experienced eye could spot.
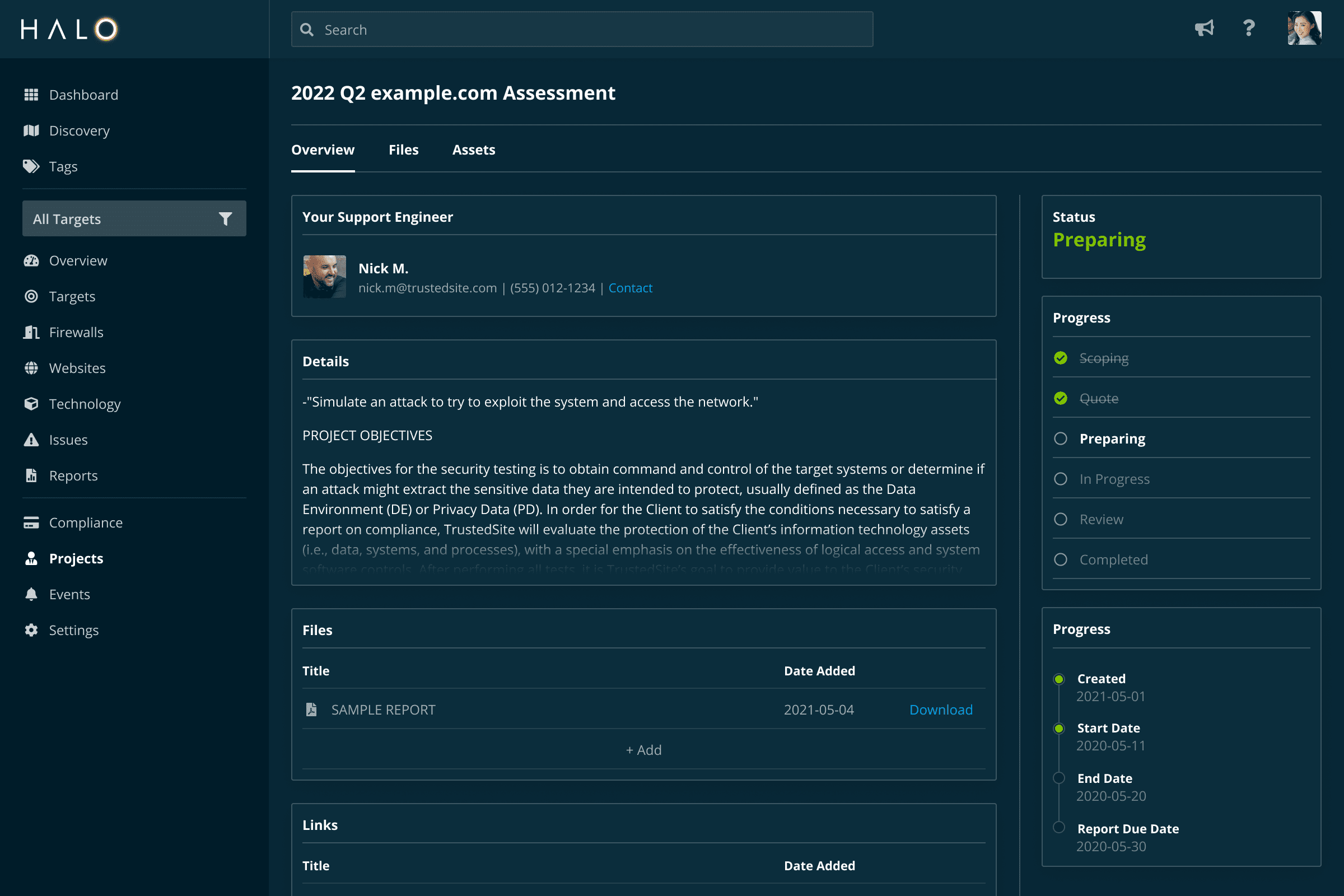
Automated and manual penetration testing are both important components of Halo Security’s unique approach to attack surface management.
With the Halo Security platform, our goal is to help you get a clear, comprehensive view of web security risks and vulnerabilities across all of your external-facing assets. We prioritize risk by severity of the threat and ease of fix, allowing you to quickly remediate the most dangerous issues. Our platform monitors your attack surface on a continuous basis, alerting you the instant an new issue arises. And with the easily discoverable issues already detected with automation, our manual penetration testers can help you find advanced risks more efficiently and at a lower cost.
Attack methods are constantly evolving, and new vulnerabilities can crop up at any time. Stay ahead of the next attack by continuously discovering and mapping your attack surface, and monitoring it for issues that leave your organization vulnerable.
Halo Security runs lightweight scans on open-source software and custom-built applications, including single page applications (SPAs) and RESTful APIs. We look for attack vectors like OWASP Top 10 Web Application Security Risks including SQL injection and cross-site scripting, as well as tens of thousands of common vulnerabilities and exposures (CVEs).
By automating security testing work, your team can spend less time looking for vulnerabilities, and more time reducing risk. Our platform checks your work for you, automatically retesting after issues have been remediated, and alerting you if any vulnerabilities remain.
With advanced reporting capabilities and clear visual dashboards, you can easily identify areas for improvement, track your progress over time and optimize your workflow. Download out-of-the-box reports or customize them to your needs for technical and compliance requirements.
Your account is fully customizable to meet your needs and preferences. Create a customized scan schedule that works with your timeline, configure user-level access privileges, and quickly scale testing services to thousands of assets. Optimize your workflow by integrating popular developer tools like Jira and ServiceNow.
When you work with Halo Security, you get a partner focused exclusively on reducing your external risk. Our experienced team of security practitioners acts as an extension of your own team, always available to help validate results, discuss new vulnerabilities, and deep dive on any asset that’s exposed to the internet.
Discover the risks across your entire attack surface with a free 7-day trial of Halo Security. With our agentless platform, you can get started in minutes and see results from day one.
Get Started FreeOr get a demo »