Eliminate unknowns.
Every external-facing asset provides attackers with another way to get inside your organization. Halo Security identifies your entire attack surface so that no threats can slip in under the radar.

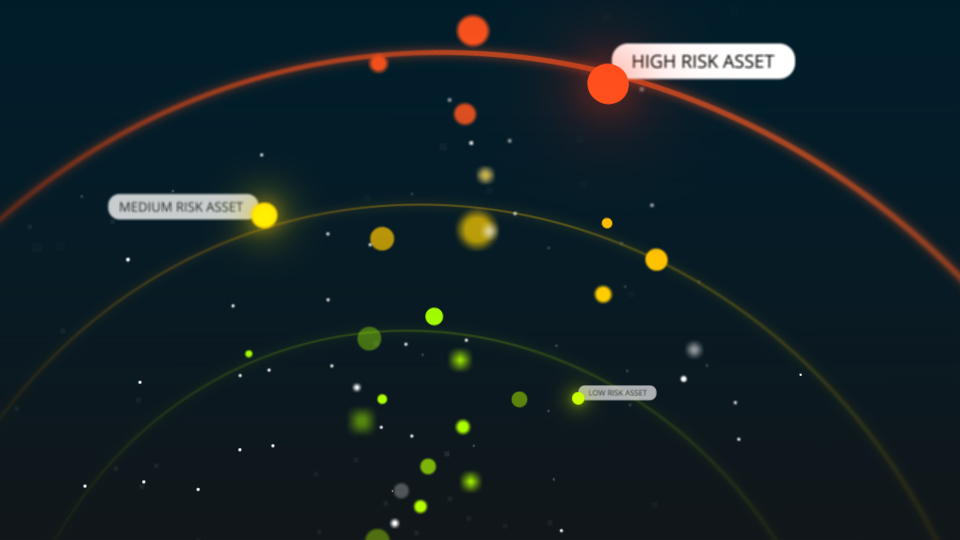
Prioritize and evaluate risk.
Halo Security’s proprietary risk scoring algorithm cuts through the noise to highlight exposures that are most attractive to attackers, helping you focus remediation efforts where they are needed most.
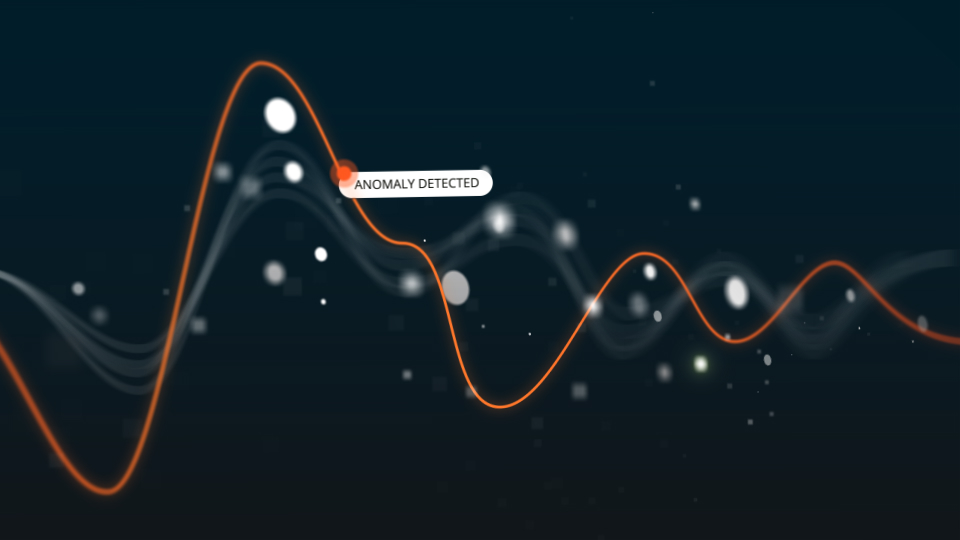
Detect changes.
Your attack surface is always evolving. Halo Security continuously monitors for changes and alerts you when something unusual arises.